Networking Basics
Computer Network is group of two or more computers connected using some form of communications technology. The communication technology can be Hub, Switch or Routers connecting the computers using cables or wireless technologies. For example, one might use a computer network connected via cables or wireless to the Internet or locally in order to gain access to a common server or to share programs, files and other information.
Computer networks can be Local Area Network (LAN) or Wide Area Network (WAN). LANs are type of networks we are connected at home or office, the name Local refers to the short geographical area coverage of the network. They commonly have very quick data transfer speeds, i.e. if you’re transferring a file from one computer to another you’ll have transfer speeds of 1000mbps or more on LAN. Control typically resides with a single organization or individual home.
WANs are networks that span a large area, commonly regional, national, or international in range. Some examples of WANs include Enterprise, government or International Organizations networks that have dedicated transmission mediums and are not open to any user out there. As with LANs, WANs are also owned by organizations and physical connectivity can be provided by external Service Providers (SPs).
the world’s largest Internetwork, the Internet, is an interlinked network of WANs and LANs. We use LANs in a home and work environment but then those LANs are connected to WANs like the Internet or a corporate network when working for international companies.
Computer networks follow certain rules and standards of communication when sending and receiving information. These are called network protocols. Information is sent in bundles, or in packet form. Different network protocols utilize specific packet transmissions, or packet switching. Network protocols also provide the means by which computers can identify each other on a network. The size and purpose of the network will determine what type of network protocol is used. Network protocols are used by servers as well as the computers they manage. Certain software applications, like web browsers, are designed to accommodate these protocols. The Defacto standard protocol for computer networks if the TCP/IP protocol.
The TCP/IP protocol suite is so named for two of its most important protocols: Transmission Control Protocol (TCP) and Internet Protocol (IP). The main design goal of TCP/IP was to build an interconnection of networks, referred to as an internetwork, or internet, that provided universal communication services over heterogeneous physical networks. The benefit of such an internetwork is the enabling of communication between hosts on different networks, even separated by a large geographical area. An Internetwork is, thus, two or more Local Area Networks (LANs) interconnected by a Router. Switches and Hubs are other networking devices; two or more computers connected to the same switch or hub (wired or wireless) are considered to be on the same network.
To be able to identify a host on a network or within an internetwork, each host is assigned an address, called the IP address. We have two standards for IP addressing, IP Version4 (IPV4) and IP Version 6 (IPV6). IPV4 uses 32 bits (four octets) written as four bytes separated by periods (full stops). They can range from 1.0. 0.1 to 223. 255. 255. 255 (this excludes reserved IP Ranges); while IPV6 uses 128 bits. [ONLY IPV4 IS DISCUSSED IN THIS ARTICLE] The IP address consists of two parts: [Network Part] [Host Part]. The network number part of the IP address identifies the network within the internet and is assigned by a central authority and is unique throughout the internet. The authority for assigning the host number part of the IP address resides with the organization that controls the network identified by the network number.
An IP address can identify a network (if the host part is all zero) or an individual host. The dividing line between the network ID and the host ID is not constant. Instead, IP addresses are split into three classes (Class A, B and C – two other classes are reserved and not discussed here) which allow for a small number of very large networks, a medium number of medium- sized networks and a large number of small networks.
Class A addresses have a first byte in the range 1 to 126. The remaining three bytes can be used for unique host addresses. This allows for 126 networks each with up to 16 million hosts. Class B addresses can be distinguished by first byte values in the range 128. 0. x. x to 191. 255. x. x. In these addresses, the first two bytes are used for the network ID, and the last two for the host ID, giving addresses for 16,000 networks, each with up to 16,000 hosts. Class C addresses are in the range 192.0.0.x to 223. 255. 255. x. Here, the first three bytes identify the network, leaving just one byte for the individual hosts. This provides about for 2 million networks of up to 254 hosts each.
It is up to the network engineer to decide (based on organizational requirements, of course!) how the subnet ID is arrived at by defining a 32- bit value called the subnet mask. This is logically ANDed with the IP address to obtain the subnet address. For example, if a subnet mask was 255.255. 255.0 and an IP address was 178. 124. 14.5, 178. 124 would identify the Class B network, 178. 124. 14 would identify the subnetwork (subnet), and 5 would identify the host on that subnet.
Addresses with Special Meanings
A network ID starting with 127 denotes the loopback interface, which is another way of specifying “this host”. The host ID part of the address can be anything in this case, though the address 127. 0.0. 1 is commonly used. Packets sent to the loopback address will never appear on the network. It can be used by TCP/ IP applications that run on the same machine and want to communicate with one another. Addresses in the range 224. x. x. x to 239. x. x. x are Class D addresses, which are used for multi- casting. Addresses 240.x. x. x to 247. x. x. x, are reserved for experimental purposes.
Net, subnet and host IDs of all binary ones (byte value 255) are used when an IP packet is to be broadcast. Three sets of addresses are reserved for private address space – networks of computers that do not need to be addressed from the Internet.
- There is one class A address (10.x. x. x),
- Sixteen class B addresses (172. 16. x. x to 172. 31. x. x), and
- 256 class C addresses (192. 168. 0. x to 192.168. 255. x)
If you have equipment which uses IP addresses that have not been allocated by InterNIC (An External IP Address Provided by ISP for Connection to the Internet) then the addresses used should be within one of these ranges.
IP Routing
How does an IP packet addressed to a computer on the other side of the world find its way to its destination? On a LAN, every host sees every packet that is sent by every other host on that LAN. Normally, it will only do something with that packet if it is addressed to itself, or if the destination is a broadcast address.
A router is different. A router examines every packet, and compares the destination address with a table of addresses that it holds in memory. If it finds an exact match, it forwards the packet to an address associated with that entry in the table. This associated address may be the address of another network in a point- to- point link, or it may be the address of the next-hop router. If the router doesn’t find a match, it runs through the table again, this time looking for a match on just the network ID part of the address. Again, if a match is found, the packet is sent on to the address associated with that entry. If a match still isn’t found, the router looks to see if a default next- hop address is present. If so, the packet is sent there. If no default address is present, the router sends an ICMP “host unreachable” or “network unreachable” message back to the sender. If you see this message, it usually indicates a router failure at some point in the network. The difficult part of a router’s job is not how it routes packets, but how it builds up its table. In the simplest case, the router table is static: it is read in from a file at start- up. This is adequate for simple networks.
TCP/IP protocol layers
TCP/IP is modeled in layers which leads to the term protocol stack. It refers to the stack of layers in the protocol suite. By dividing the communication software into layers, the protocol stack allows for division of labor, ease of implementation and code testing, and the ability to develop alternative layer implementations. Layers communicate with those above and below via concise interfaces. In this regard, a layer provides a service for the layer directly above it and makes use of services provided by the layer directly below it. For example, the IP layer provides the ability to transfer data from one host to another without any guarantee to reliable delivery or duplicate suppression. Transport protocols such as TCP make use of this service to provide applications with reliable, in-order, data stream delivery. (See below figure)
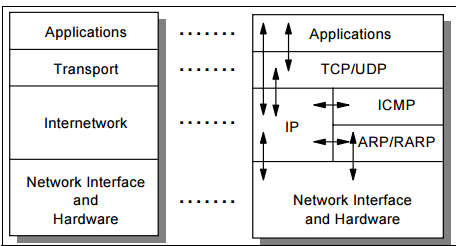
Figure: The four layers of TCP/IP Reference Model
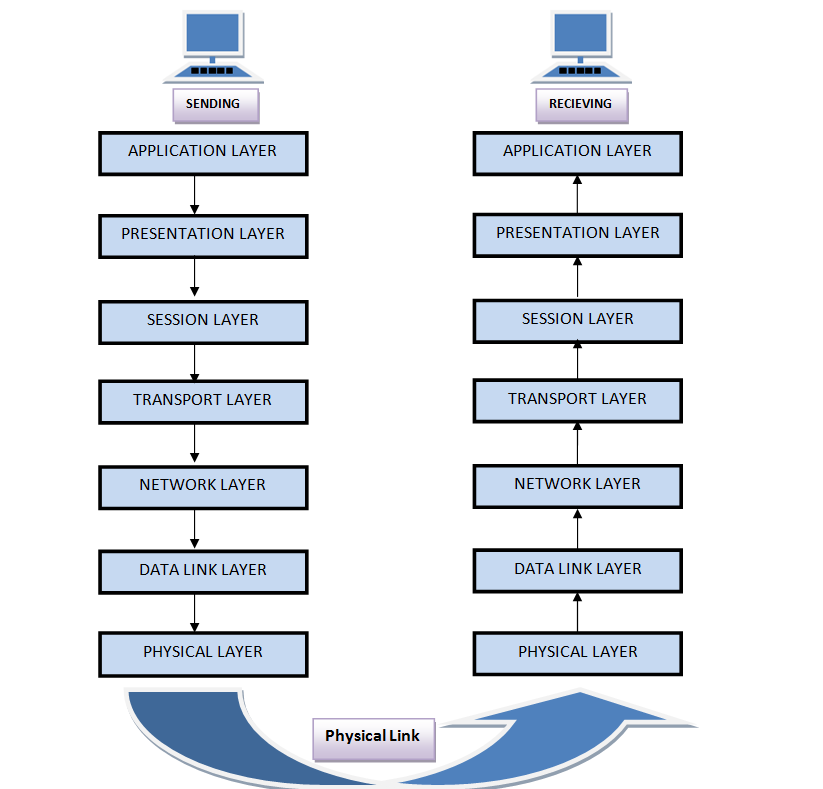
Figure: The ISO/OSI 7 layers Reference Model
Application layer
The application layer is provided by the program that uses TCP/IP for communication. An application is a user process cooperating with another process usually on a different host (there is also a benefit to application communication within a single host). Examples of applications include Telnet and the File Transfer Protocol (FTP).
Transport layer
The transport layer provides the end-to-end data transfer by delivering data from an application to its remote peer. Multiple applications can be supported simultaneously. The most-used transport layer protocol is the Transmission Control Protocol (TCP), which provides connection-oriented reliable data delivery, duplicate data suppression, congestion control, and flow control.
Internetwork layer
The internetwork layer, also called the internet layer or the network layer, provides the “virtual network” image of an internet (this layer shields the higher levels from the physical network architecture below it). Internet Protocol (IP) is the most important protocol in this layer. It is a connectionless protocol that does not assume reliability from lower layers. IP does not provide reliability, flow control, or error recovery. These functions must be provided at a higher level. IP provides a routing function that attempts to deliver transmitted messages to their destination.
Network interface layer
The network interface layer, also called the link layer or the data-link layer, is the interface to the actual network hardware. This interface may or may not provide reliable delivery, and may be packet or stream oriented. In fact, TCP/IP does not specify any protocol here, but can use almost any network interface available, which illustrates the flexibility of the IP layer.
Some windows network diagnostic commands
The following are common Microsoft Windows Network commands
ipconfig
Ipconfig is a Console Command which can be issued to the Command Line Interpreter (or command prompt) to display the network settings currently assigned to any or all network adapters in the machine. This command can be utilised to verify a network connection as well as to verify your network settings.
netstat
Displays active TCP connections, ports on which the computer is listening, Ethernet statistics, the IP routing table, IPv4 statistics (for the IP, ICMP, TCP, and UDP protocols), and IPv6 statistics (for the IPv6, ICMPv6, TCP over IPv6, and UDP over IPv6 protocols). Used without parameters, netstat displays active TCP connections.
tracert
The tracert command is used to visually see a network packet being sent and received and the amount of hops required for that packet to get to its destination.
Users with Microsoft Windows 2000 and Windows XP who need additional information network latency and network loss should also consider using the pathping command.
ping
Helps in determining TCP/IP Networks IP address as well as determine issues with the network and assists in resolving them.
telnet
Telnet is software that allows users to remotely access another computer such as a server, network device, or other computer. With telnet users can connect to a device or computer, manage a network device, setup a device, transfer files, etc.
ftp
FTP is short for File Transfer Protocol, this page contains additional information about the FTP command and help using that command in Unix and MS-DOS (Windows).
net
The net command is a Command Prompt Command that can be used to manage almost every aspect of a network and its settings including managing network shares, network print jobs, network users, and much more.
Some net commands:
Net Computer – The net computer command is used to add or remove a computer from a domain.
Net config – show information about the configuration of the Server or Workstation service.
Net share command is used to create, remove, and otherwise manage shared resources on the computer
Net start command is used to start a network service or list running network services
Net statistics command is used to show the network statistics log for the Server or Workstation service (e.g. net statistics server – shows server statistics – including when the server is last rebooted)
route
The function and syntax of the Windows ROUTE command is similar to the UNIX or Linux route command. Use the command to manually configure the routes in the routing table.
Route add
route –p add <host or network IP> mask <subnet mask> <ip to which route will be forwarded>
e.g. route –p add 10.23.0.0 mask 255.255.0.0 192.168.7.20 – this configuration will send all requests to the network 10.23.0.0 /24 to the host port 192.168.7.20 (this should be)
Route delete
e.g. route delete <host or network IP>
Route Print – Prints to screen all configured route forwarding
arp
Displays, adds, and removes arp (address resolution Protocol) information from network devices.
nslookup
Displays information that you can use to diagnose Domain Name System (DNS) infrastructure. Before using this tool, you should be familiar with how DNS works. The Nslookup command-line tool is available only if you have installed the TCP/IP protocol.
